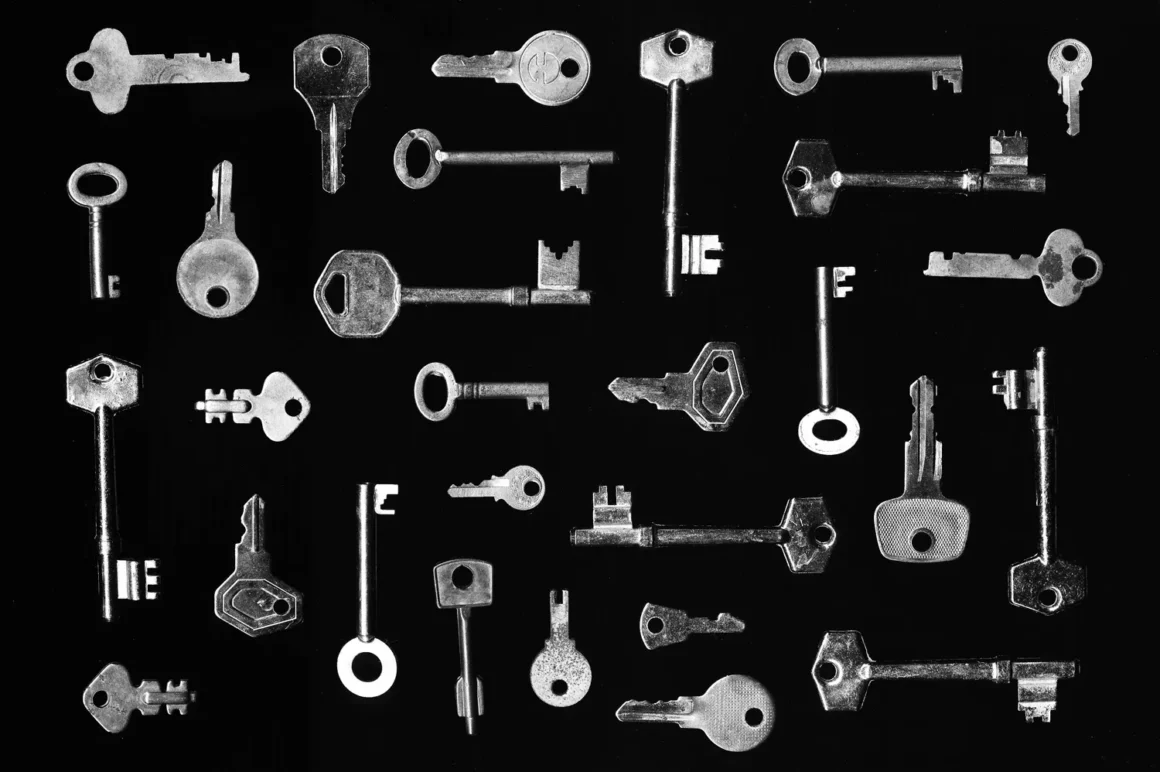
The God Mode of Cyberwarfare
Finding a zero-day is like stumbling upon a secret passage in the world’s most secure vault. It is the closest thing hackers—whether criminal, state-sponsored, or merely curious—get to “God…
The things we know and the things we don’t know we don’t know.
Right, strap in, because this one’s a bit of a mental workout. Donald Rumsfeld’s famous “known knowns” speech has been the subject of endless debate, analysis, and, let’s be honest, a fair bit…
Parental Oversight Online: Not Helicoptering.
When it comes to parenting in the digital age, many parents face a psychological trap: they equate monitoring their child’s online activity with overprotectiveness. This is a mistake—one…
Lattes or Firewalls? Your Choice.
Right, let’s get this straight: If you’re spending more on fancy coffee than on cybersecurity, you might as well leave your front door wide open with a big neon sign that says “Help Yourself.”…
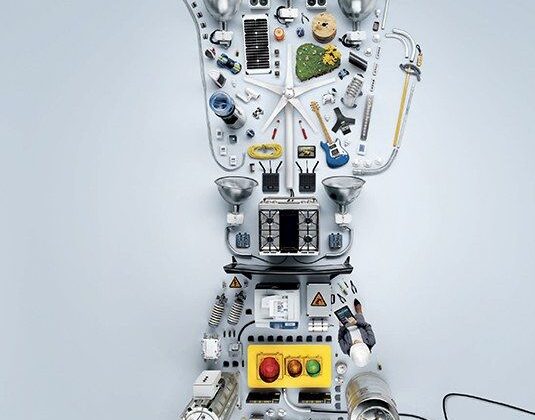
Welcome to the Internet of Terrifying Things
Right, so we’ve all seen it coming—the Internet of Things, where every single device is online, from your thermostat to your toaster to your grandmothers pacemaker. Sounds convenient, doesn’t…
Why North Korea Is Nearly Immune to Cyber War
Now, when you think about cyber warfare, you probably imagine some Hollywood-esque scenario—hackers in hoodies furiously typing away, firewalls crumbling like soggy biscuits, and some bloke in…
When the Battlefield Extends Beyond the Keyboard
For years, cybersecurity was seen as a digital arms race—hackers versus defenders, code against code, exploits against patches. The battlefield was virtual, confined to servers, networks, and…
To Save Everything, Click Here: Why Not Everything Can Be Solved
We love solutions. We love the idea that every problem—no matter how complex—has an answer, waiting to be uncovered by the right logic, the right technology, or the right expertise. This…
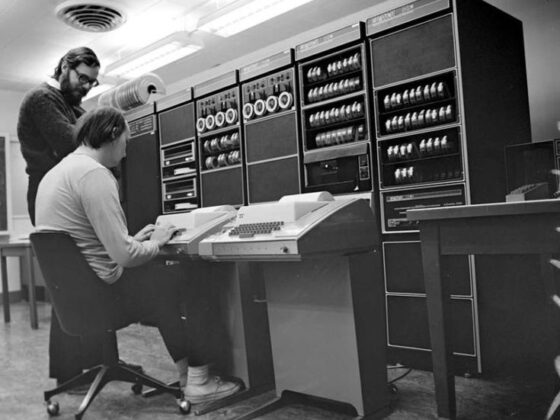
The Accidental Naming of UNIX: A Security Researcher’s Joke That Stuck
The history of UNIX is filled with moments of ingenuity, but its name itself comes from an unexpected source—a joke. In the late 1960s, when Ken Thompson was developing an early version of the…
Recent Comments
No comments to show.
The Unseen Innovators: Why Security Needs to Assume the Unexpected
In the world of cybersecurity, it’s easy for developers, security experts, or system architects to slip into a false sense of security. When someone says, “Nobody will go to the trouble…
Cyberwar: The Next Evolution of Conventional Warfare
In the 21st century, warfare is no longer confined to the traditional domains of land, air, and sea. As technology evolves, so too does the nature of conflict. Today, cyberwar is not a…
Penetration Testing: Reducing Uncertainty, Not Changing Reality
A common misconception about penetration testing is that it somehow “hardens” security simply by being performed. But a penetration test doesn’t directly alter the security of an…